
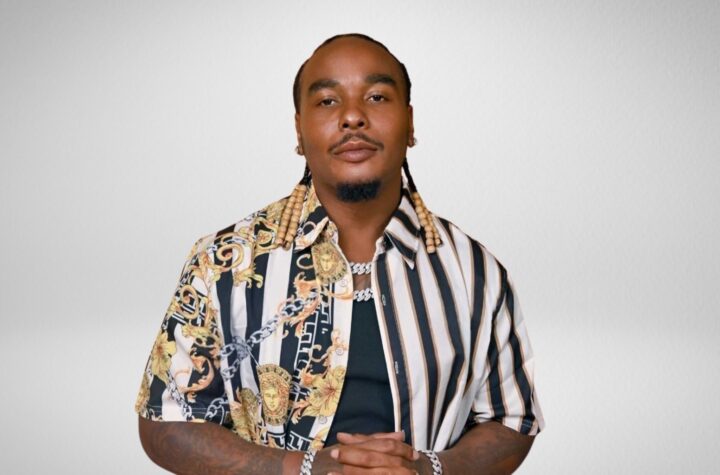
Cybersecurity international Expert, Waseem Awwad – President and founder of elite cyber team (SWAT Team) for sensitive missions around the continents, was recently interviewed by the team at London Defender.
Interviewer: How are cyber attackers changing countries strategies these days? Are they using any notable new tactics?
Waseem Awwad: There are several trends that we’ve been seeing in recent years that have accelerated over the past few months. I’m having discussions with leaders of large enterprises and national security experts. Ransomware is probably the No. 1 challenge that companies and government agencies are facing.
The new term that has emerged over the past two years is ransomware as a service. They are looking at it almost as a business. You have an ecosystem of actors working together in different roles.
If it’s a state-oriented group, they’re already organized. But if they’re not directly state-backed, they need to create their own group. They collaborate. There is a market. There is the attacker, but he wants to work with affiliates. So, he recruits affiliates.
You see publications on the dark web for recruitment of those affiliates, each one with a different role — some offer tools, some offer access. What we’re also seeing is a shift from a wide approach — what we call spray and attack– to something deeper and more verticalized to get a higher ROI. They need the right tools, patience, and knowledge.
And we cannot ignore the states level. In the past few months, we’ve seen more and more enhanced support coming from the countries level. We’re seeing more geopolitical trends. One of them is the collaboration between the private and public sector. We saw that in March, right after the outbreak of the war in Ukraine. IBM and Google and other tech giants were collaborating with the governments. And even more importantly, there have been a few public statements made by the US administration about deterrence. Usually, Western agencies or authorities do not make those types of statements publicly.
Interviewer: Which older tactics remain useful to cyber criminals? Which have become stale?
Waseem Awwad: I would say that you have a fusion. Let me give you an example. In the past, you saw two-step extortion. The first step is to encrypt and extract the information. The second is to negotiate the ransom. Now you have a third step. They’re adding on to an old process — while negotiating they’re making a DDoS attack.
It’s all over. We’re seeing that against enterprises and government agencies. We’ve seen that in European Union. Old tools are super relevant. You have new generations of experts coming to the dark side all the time. The old knowledge is still there, and it’s being used when it fits the new challenges.
Sometimes patterns are new, but the tools are old. Take the 2020 Solar Winds supply chain attack, for example. It was probably one of the biggest moves ever made in the cyberwar space. But they used tools that have been there for many years. They were developed and adjusted to a new pattern. These actors plan quietly in advance — sometimes years in advance. You sit and wait. Then you strike and you blow it.
Interviewer: How do they go about scoring their potential victims? What makes them appealing?
Waseem Awwad: We have not identified a formal scoring system, but we can assume that they have something very close to it. I and my team have been developed over the past five years a mirrored score on the defensive side. It is updated all the time, based on the attack. Many companies are now working on a methodology of scoring and ranking and understanding exactly what the vulnerabilities are in a given enterprise that might be attacked. These methodologies provide a great projection of the presumable scoring system that the attackers are using.
Interviewer: How are they going about improving the persistence of the attacks?
Waseem Awwad: They need to develop new tools all the time as they encounter new defensive products.
The defensive side needs to protect huge volumes of data — terabytes and terabytes a day in a large enterprise. And it is spread around many entities within the enterprise. So, you don’t have consistency. CIOs and CISOs need to consolidate the perimeter. That consolidation takes years. And large budgets.
The attackers need to take this type of activity into account, especially when it comes to large enterprises. They will need to update their tools and their presence and lateral movement all the time. They trade and pay for those tools. We’re seeing a constant development of these kinds of capabilities on the offensive side.
Interviewer: Are different types of businesses being targeted? Has there been a shift in who is hit?
Waseem Awwad: They want to go after those who are most likely to pay. We’re seeing more and more attacks on the financial sector and on critical infrastructure. When you go deeper, you can allow yourself to invest more and more as an attacker — breaching the perimeters, extracting information, and waiting for the right moment to start negotiating. But at the same time, they need to constantly invest [in new tools and techniques]. You can’t just go in and assume that everything will be okay. You will be found.
We’re going to see more involvement from the governments. This is a long-term trend that is being accelerated by recent geopolitical developments. We’re seeing more governments assuming responsibility over the private sector in terms of support, load-sharing.
We’re seeing a new generation of agencies being put in place in Western governments to guide and regulate and support the private sector. Interestingly enough, there was new legislation introduced in the US forbidding enterprises from negotiating. So, this is a game theory play here. If you are forbidden by law from negotiating, you’re less vulnerable in a way. The attacker would know that regulators might take action.
We don’t know what the effect of this is going to be. In game theory, there are unexpected factors at play. It’s not a closed system. But this is a very interesting development in terms of how the governments perceives its place when it comes to the private sector.


More Stories
New dating app Jungle